
For over a decade, we’ve reported on and used a DDoS attack type we call „THOR“ (as it strikes like Mjölnir), known also as Burst/Short-Burst or Tsunami attacks.
Now that these tactics are widespread and reported by nearly every major vendor, it’s time to revisit why they remain so devastating—and to shed light on how their high-impact, short-duration nature makes defense exceptionally difficult by exploiting critical gaps in detection and mitigation.
What Are Pulsewave DDoS Attacks?
Pulsewave DDoS attacks are characterized by repeated, intense surges of malicious traffic delivered in brief intervals, rather than a continuous barrage. Unlike conventional volumetric attacks that maintain steady pressure, these bursts are designed to „hit and run,“ overwhelming defenses before automated or manual responses can fully engage.
The term „Pulsewave“ derives from electronic music and describes the behavior of sound generators (oszillators) who can usually create sine waves, sawtooth waves or pulsewaves.
In DDoS this behavior specifically describes a pattern where traffic pulses in clockwork-like succession—high-volume bursts lasting seconds to minutes,
followed by pauses. This pulsing mechanism allows attackers to maximize the efficiency of their botnets, pinning down multiple targets by alternating bursts across different victims.
0:00
Pulsewave in our DDoS Simulator
A key innovation in these attacks is their ability to exploit inherent delays in DDoS mitigation appliances and cloud-based scrubbing services. For instance, hybrid defenses that rely on on-premise hardware for initial detection often require time to analyze traffic and divert it to cloud mitigation— a window that short bursts deliberately target.
Characteristics of Short Burst Attacks
Short burst attacks exhibit several distinct traits that set them apart from traditional DDoS methods (the example below explains layer 7 attacks, but the individual points also apply to volumetric attacks)
- Duration and Intensity: Most bursts didnt last long, with many concluding in mere seconds. Despite their brevity, they can achieve staggering requests per seconds that can cause service impacts
- Avoid Attack Detection: Because the pulse duration is shorter than the detection threshold, the attack can overwhelm a target without raising alarms or activating mitigations. By stopping prematurely, attackers avoid extended monitoring from tools that depend on ongoing patterns to trigger alerts, enabling the initial disruption to continue without engaging automated protections.
- Pulsing Pattern: Traffic arrives in synchronized waves, exploiting e.g. overflow of TCP session tables to cause intermittent packet loss on firewalls or real service impacts on backends, if the traffic passes through.
This pattern can be randomized or periodic, making prediction difficult. - Multi-Vector and Adaptive Nature: Attacks frequently combine different attack vectors (e.g., GET/RANDOM/POST-Floods, Slowloris, TCP Handshales), and adapt payloads to evade signature-based detection.
- Botnet Utilization: Attackers use botnets like AISURU to generate bursts, allowing efficient resource allocation across targets without exhausting the network. Combined with a proxy-service, such an attack can become a real problem for the blue team
The following diagram illustrates a typical Pulsewave attack sequence against a Website/API, showing how bursts disrupt normal operations and mitigation processes:
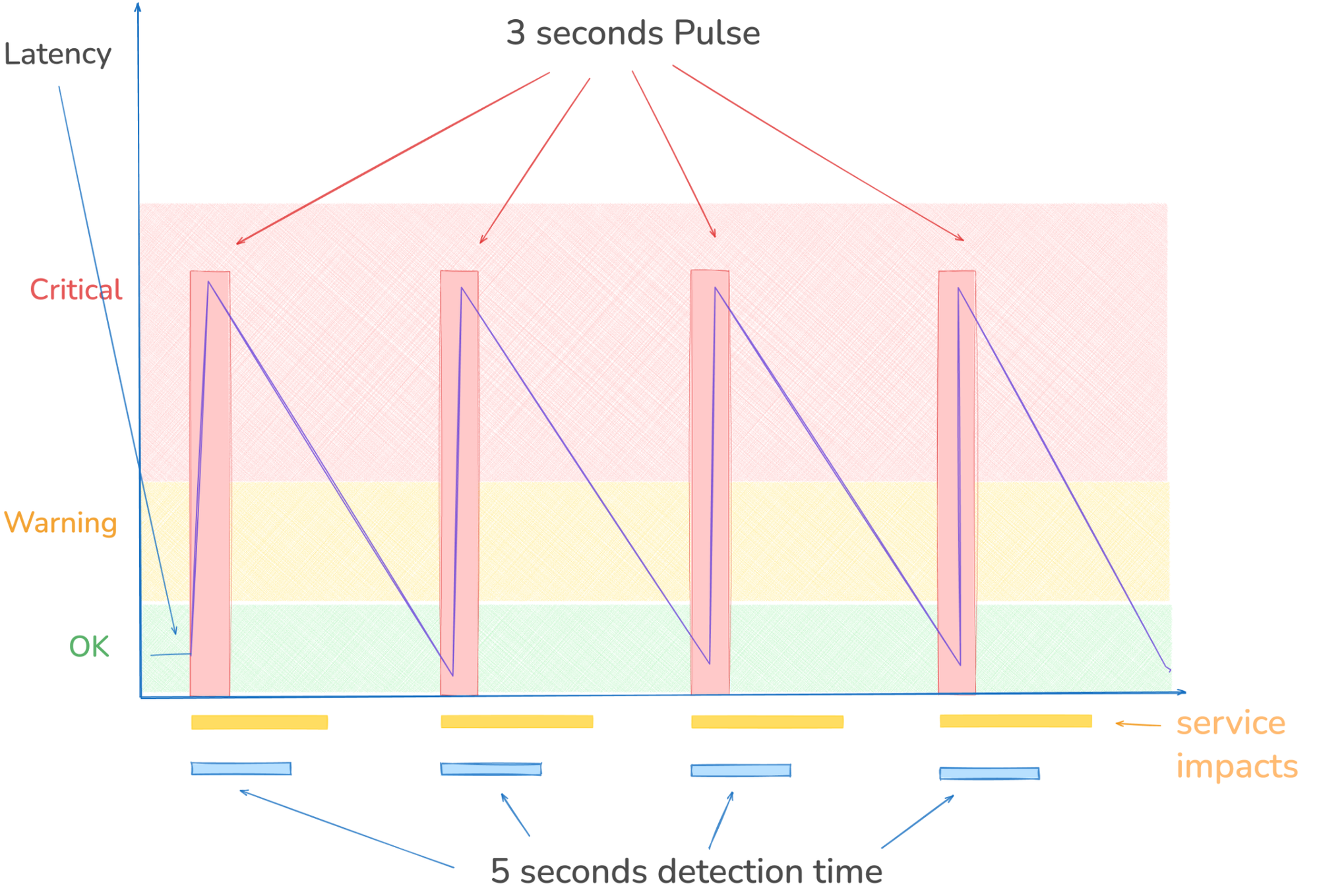
- Pulse lasts shorter (3 seconds) than the detection time, thus is not detected or mitigated
- payload passes to the backend, causing immediately a service impact
- service recovery starts, when the first wave is stopped; after 5 seconds the service is back online (8 seconds total after attack start)
- after 15 seconds the next wave starts for 3 seconds with the same impact as above
- with this pattern we achieved service impacts für 50% of the time, which is enough for many systems to make them unusable due to connection resets or packet loss
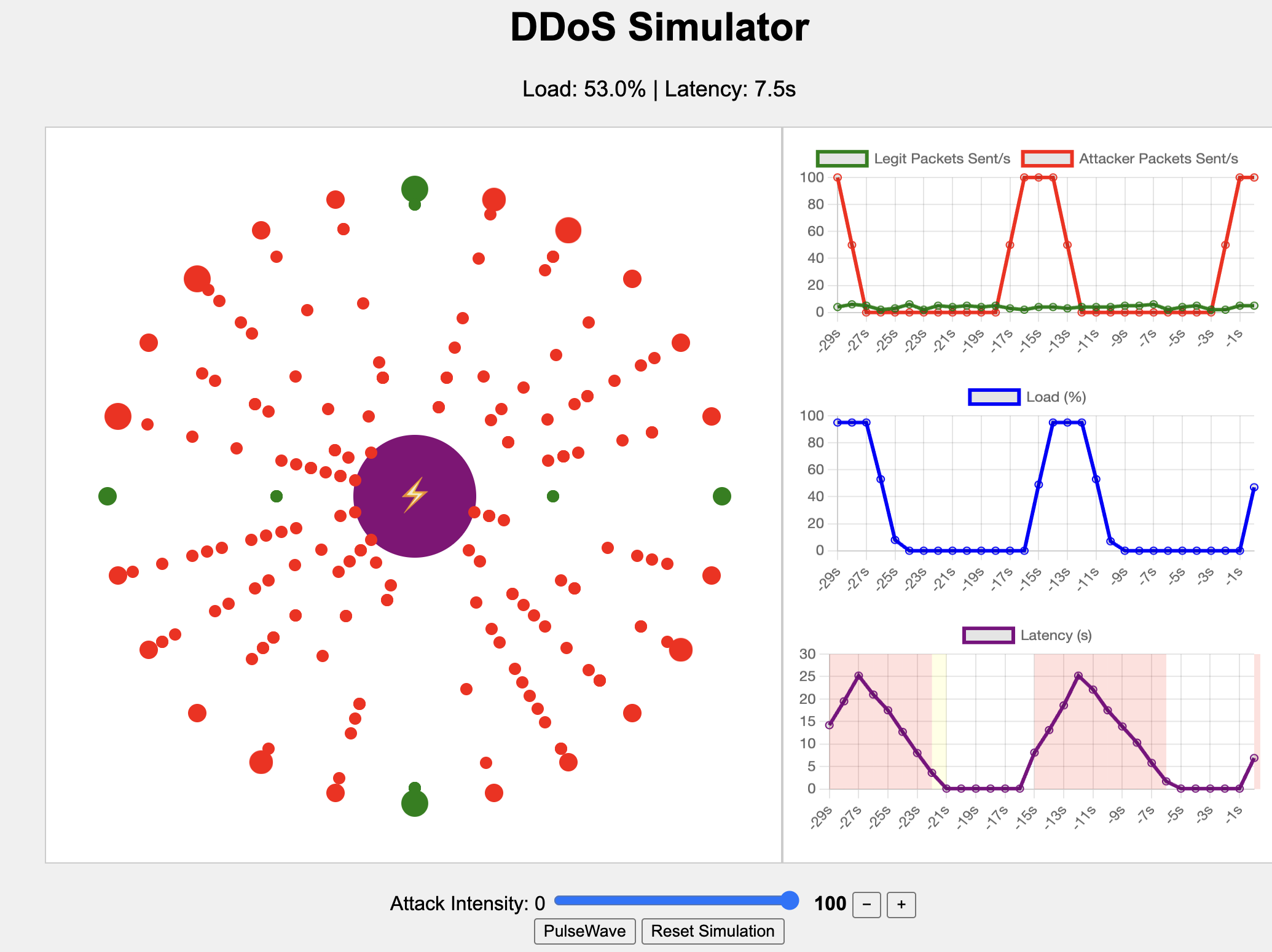
In our simulation we see the same pattern:
Mitigation Strategies
Defending against short burst attacks requires proactive, layered approaches:
- Inline Protection: Deploy always-on, inline DDoS mitigation that detects and blocks bursts in real-time without diversion delays, usable for volumetric attacks
- Rate Limiting: destination based rate limiting can protect the origin. While it may cause some service impact during the attack, the recovery phase is much smaller, and triggering the mitigation with an alert might give the blue team valuable information about an ongoing attack
Source based rate limiting might work well against smaller botnets, but can be bypassed with proxies (layer 7) or IP-spoofing (volumetric) - Captchas and Browserchallenges: Works well against IoT-Bots attacking complete websites, but can be rendered useless when protecting APIs
- Simulation and Testing: Regularly test defenses with tools simulating pulse-wave scenarios, such as those from zeroBS
Notable Examples and Trends
Short burst attacks have surged in prevalence since the early 2020s. In 2021, Microsoft Azure reported that 57% of mitigated attacks lasted 30 minutes or less, with multi-vector bursts remaining common. By 2023, NETSCOUT noted two-thirds of global DDoS incidents were under 15 minutes, reflecting a strategic shift to test defenses with minimal effort.
A landmark event occurred in December 2025 when Cloudflare mitigated a 29.7 Tbps attack from the AISURU botnet, lasting just 69 seconds but causing prolonged operational fallout.
Trends show increasing sophistication, with attacks originating from regions like Indonesia and integrating with multi-stage strategies. As of 2024-2025, short bursts accounted for the majority of incidents, with average durations rising to 45 minutes overall but emphasizing quick, disruptive jabs.
Please find details on these types of attacks in the following reports:
- Cloudflare / 2025 Q1 DDoS Threat Report
4.8 Billion PPS for 10 seconds
https://blog.cloudflare.com/ddos-threat-report-for-2025-q1/ - DDoS on Repeat: Measuring Pulse-Wave DDoS in the Wild
https://thomasez.folk.ntnu.no/itc36/itc2025-final8.pdf - DDoS Guard / Global DDoS Trends: 2025 Mid-Year Report
mentioned pulsewave attacks as trend for 2025
https://ddos-guard.net/blog/ddos-trends-2025-mid-year - Netscout / Top 9 Challenges Associated with DDoS Mitigation Efforts
„Short-burst/rapid-fire attacks that exploit long detection times“
https://www.netscout.com/blog/top-9-challenges-associated-ddos-mitigation-efforts - Imperva / Early 2025 DDoS Attacks Signal a Dangerous Trend in Cybersecurity
Post Mortem for an attack that used pulsewave pattern
https://www.imperva.com/blog/early-2025-ddos-attacks-signal-a-dangerous-trend-in-cybersecurity/ - Radware / DNSBomb Pulsing DoS Attack https://www.radware.com/security/threat-advisories-and-attack-reports/dnsbomb-pulsing-dos-attack/
- Distributed Pulse-Wave Simulator for DDoS Dataset Generation
(scientific paper)
https://arxiv.org/html/2511.12774v1 - zeroBS / THORS Hammer: a destructive DDoS Attack Method
https://blog.kybervandals.com/thors-hammer-a-destructive-ddos-attack-method/ - Bleeping Computers / Pulse Wave – New DDoS Assault Pattern Discovered
https://www.bleepingcomputer.com/news/security/pulse-wave-new-ddos-assault-pattern-discovered/
Happy Fragging!





